In the humid corridors of Barbados’ public service, there is a new buzzword circulating with the frequency of a tropical breeze: “GovTech.” Established in late 2023 with the high-octane promise of dragging a paper-clogged bureaucracy into the 21st century, GovTech Barbados Ltd. was heralded as the “silver bullet” for the nation’s digital woes.
However, as we move through 2026, the initial honeymoon period has ended. While the PR machinery hums with talk of “AI-powered prototypes” and “digital champions,” the average Barbadian citizen is still standing in physical lines, clutching paper forms, and wondering when the promised “sweeping transformation” will actually increase the ease of doing business.
The reality is that GovTech Barbados, despite its modern branding and high-profile leadership, is currently a victim of institutional inertia, misplaced priorities, and a “startup” culture that is fundamentally incompatible with the weight of government bureaucracy.
The Prototyping Trap: Appearance vs. Reality
The most visible “achievement” of GovTech Barbados so far has been the rollout of rapid “prototyping.” Using AI to turn a paper form into a digital interface in “minutes” sounds like a revolution. It makes for excellent LinkedIn posts and impressive demos for the Ministry of Industry, Innovation, Science and Technology (MIST).
But a prototype is not a service.
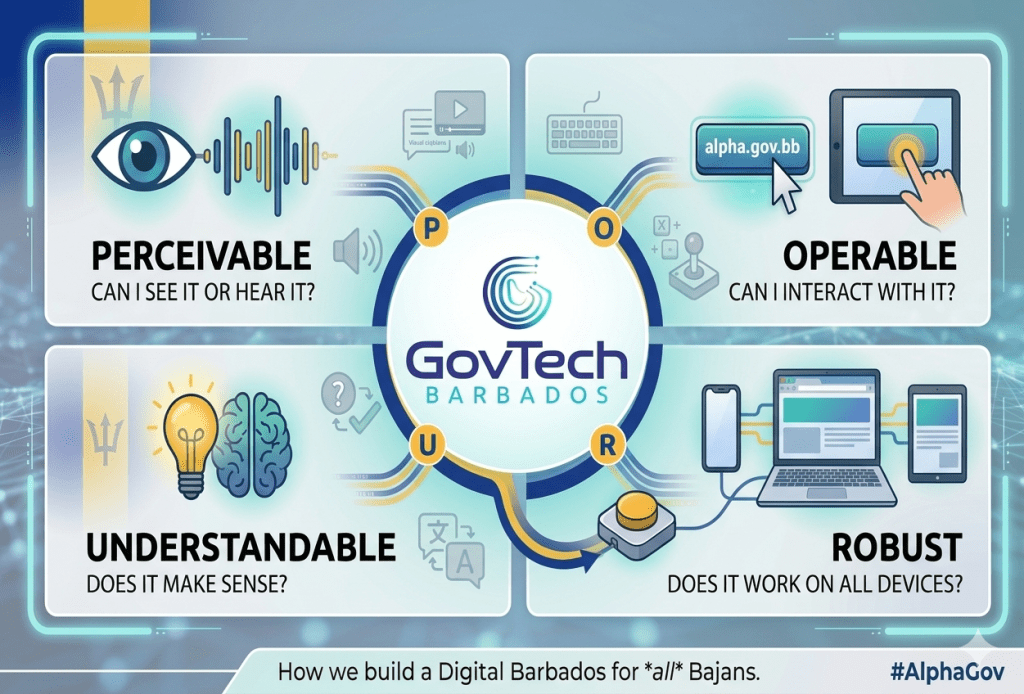
The “Prototyping Trap” occurs when an organization prioritizes the UI (User Interface) over the UX (User Experience) and the underlying backend processes. Turning a paper form into a digital PDF or a web form is the easiest 5% of digital transformation. The difficult 95% involves:
- Integrating with the national identity system.
- Automating backend approvals so a human doesn’t have to print the digital form to file it.
- Introducing workflow management tooling to handoff tasks between different government departments or control points.
- Updating the 40-year-old legislation that still requires a physical signature.
By focusing on what they believe to be “tangible outputs” to win public confidence, GovTech is essentially painting the windows of a house that has no plumbing. Citizens may fill out a form online, but if the “transformation” stops there, the inefficiency is simply moved from the front counter to a back-office inbox. Instead of focusing on throughput (how many forms can we digitize?), GovTech Barbados needs to focus on outcomes (how much time and money can we save the citizen?). It’s also quite telling that the GovTech team has neither the deep expertise nor a visible focus on ICT law and business process reengineering.
The CEO Dilemma: A Startup Mindset in a “Legacy” Environment
Mark Boyce, hired in July 2024, has brought a seemingly more tech savvy energy to the role. His background, marked by a vocal critique of the “safe” career paths of doctors and lawyers in Barbados, suggested he was the disruptor the island needed. However, in reality, Mr. Boyce does not have the qualifications or experience to lead a major national digital transformation initiative like GovTech Barbados. He has never led complex enterprise or government implementations which include cloud computing, interoperability layers, cybersecurity, e-commerce, digital identity, and big data. Unfortunately, neither has the majority of his key hires.
Digital transformation in a government setting is less like a tech startup and more like an organ transplant. The “host body” (the existing Civil Service) often rejects the “new organ” (GovTech) if the cultural and legislative prep work isn’t done.
I can’t help but to think that GovTech is operating as an isolated island of innovation. While Boyce and his team speak the language of “The Radical How” and “agile execution,” the rest of the government still speaks the language of “The General Orders” and “Financial Rules.” This cultural mismatch has led to a bottleneck where GovTech builds prototypes that sit in limbo for months because the “human review process” in traditional ministries remains unchanged.
The Sovereign Cloud and the “Hardware Hubris”
One of GovTech’s early and most controversial claims was that Barbados was “on the brink” of a sweeping transformation fueled by a Tier 3 data center and a “sovereign cloud.”
As I noted in a previous blog post, this often feels like “déjà vu.” Barbados has a history of announcing expensive infrastructure projects that fail to deliver service-level improvements. It’s important to note that:
- Costs are astronomical: A greenfield Tier 3 data center can cost upwards of $20 million in capital expenditure, with millions more in annual operating costs.
- Infrastructure vs. Service: A data center is just a room with servers. If the software running on those servers is poorly designed or the data remains siloed in different ministries, the “Sovereign Cloud” is just a very expensive local hard drive.
Furthermore, the focus on building local infrastructure ignores the global trend toward public cloud utilization (AWS, Azure, Google Cloud), which offers better security, scalability, and disaster recovery than a small island nation can typically manage on its own. The obsession with “sovereign hardware” often masks a lack of “sovereign software” capability.
A better approach would be a hybrid cloud model with a smaller footprint sovereign data center hosting “mission critical” and “secret” data (e.g., Digital ID, Electronic Patient Records, BimPay, etc.) and leveraging the public cloud for non-sensitive, high-scale applications (e.g., public-facing websites, information portals).
Missing the “Human” in the Human Firewall
For a “GovTech” agency, there has been a glaring lack of focus on the digital literacy of the civil service. Digital transformation is 10% technology and 90% people.
While GovTech talks about “Digital Champions” within ministries, these individuals are often overstretched civil servants with no formal technical training and no authority to change the processes they are “championing.” Without a massive, nationwide upskilling program for the thousands of government workers who actually process the forms, GovTech’s tools will remain shiny toys that no one knows how to play with.
The Transparency Deficit
Meaningful digital transformation requires trust. Yet, GovTech Barbados must be questioned for its approach to:
- Cybersecurity: Barbados continues to score poorly on the ITU Global Cybersecurity Index. Announcing “AI-powered” government services without a robust, transparent cybersecurity framework or government-wide AI governance standard is a recipe for a national data disaster.
- Data Protection: As GovTech moves to “release public datasets” to spur local tech growth, there are unanswered questions about how citizen privacy is being protected under the Data Protection Act. Where is the Open Data Policy? What about Freedom of Information (FOI) legislation? What will be the overarching data governance framework? Is the Data Protection Commissioner being continuously engaged?
- Procurement: Is GovTech empowering local startups, or is it becoming a middleman for expensive foreign “turnkey” solutions that don’t fit the local context?
- Digital Identification: Considering the existence of the Trident ID system, why haven’t centralized and federated digital ID been prioritized? GovTech should have already built a “Single Sign-On (SSO)” for all government portals. Instead of having separate logins for Taxes (TAMIS), NIS, and the Land Registry, a citizen uses one verified Trident identity. GovTech can also act as a “Trust Broker.” For example, local banks should be mandated to use the Trident ID API to verify a new customer’s identity instantly, rather than requiring them to visit a branch with a passport. Banking customers should also be able to login to their Internet and mobile banking applications with the Trident digital ID.
Notwithstanding a clear lack of transparency, GovTech Barbados has been granted a multi-million dollar budgetary increase in the 2026–2027 Estimates. The public must now ask: how is this agency being held accountable for its results – or the evident lack thereof?
The Verdict: Is it Transformation or Decoration?
As of early 2026, GovTech Barbados has achieved Digital Decoration. It has made the government look more modern, but it hasn’t made it work more efficiently.
For GovTech to move from a PR success to a systemic success, it needs to stop focusing on “tangible prototypes” and start doing the “unsexy” work of:
- Legislative Reform: Working with the Attorney General to kill the “physical signature” requirement once and for all.
- Interoperability: Forcing ministries to share data through a central API, so citizens don’t have to provide their birth certificate to five different departments.
- Radical Transparency: Publishing real-time KPIs on service delivery times, not just “how many forms we digitized.”
If GovTech continues down its current path, it risks becoming just another “State-Owned Enterprise (SOE)” – a well-funded agency that produces beautiful reports and prototypes while the people of Barbados continue to wait in the sun for a service that should have been a website click years ago.



