Introduction
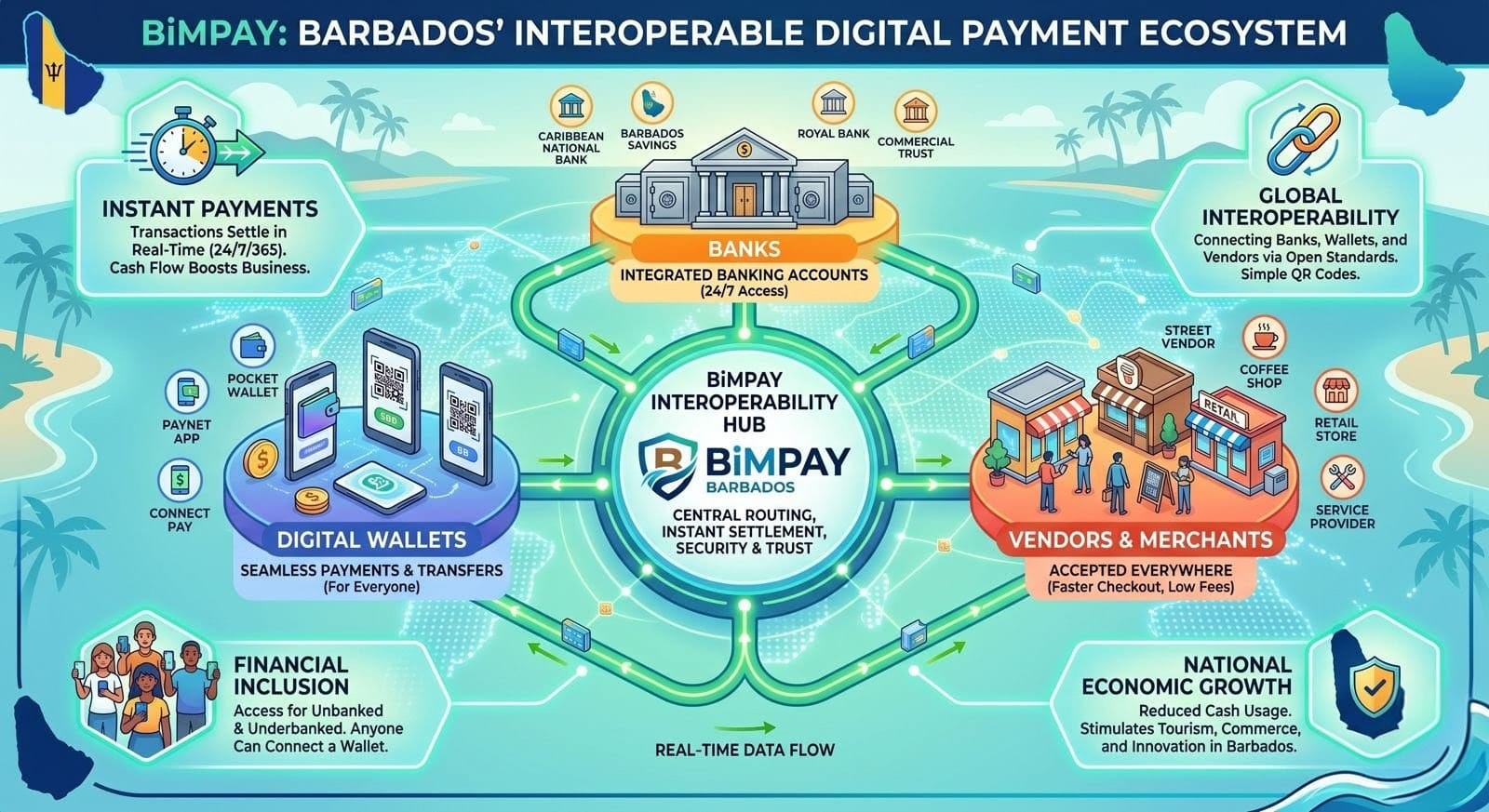
On June 12, 2026, the Central Bank of Barbados (CBB) will launch BiMPay, a national Instant Payment System (IPS). While the Caribbean has seen high-profile struggles with Central Bank Digital Currencies (CBDCs), specifically the Bahamas’ Sand Dollar, Jamaica’s JAM-DEX, and the Eastern Caribbean’s DCash, BiMPay arrives with a different structural approach.
BiMPay is not a new currency; it is a payment platform designed to facilitate 24/7/365 transactions between existing banks and digital wallets. However, because BiMPay utilizes digital wallets to reach the unbanked, it faces the same “adoption wall” that stalled its regional neighbors. To ensure BiMPay becomes a fixture of daily life rather than a technical footnote, the Government of Barbados must learn from the failures of the prior wave of digital currencies.
Bridging the Gap: Make It Better Than Cash
The regional landscape is a graveyard of “technically sound” projects that failed to reach critical mass.
- The “Utility Conundrum” (Sand Dollar & JAM-DEX): In the Bahamas and Jamaica, users often asked, “Why do I need this?” If it takes longer to operate the app than to hand over a $10 bill, cash remains king.
- The “Merchant Friction” (DCash): Merchants were often treated as an afterthought, forced to adopt new hardware or navigate complex settlement delays.
- The “Trust Deficit”: In several jurisdictions, citizens feared government surveillance of their transactions, leading to a wait and see approach that effectively killed momentum. There is also a deep mistrust across the region when it comes to privacy and security protections in online services, which significantly hampered uptake.
- The “Onboarding Hurdle”: The enrollment phase must be virtually seamless. Traditional digital wallets require cumbersome identity verification to comply with anti-money laundering regulations. By hooking BiMPay’s onboarding process directly into the Trident ID framework, the system could instantly verify a citizen’s identity remotely via a mobile device.
BiMPay must solve a burning problem for the average citizen. This means moving away from abstract goals like “financial inclusion” and focusing on Instant Settlement, the ability for a street vendor or a ZR driver to receive funds and use them to buy supplies ten seconds later.
Solve the “Merchant Friction” Problem
In Jamaica and the Eastern Caribbean, adoption was crippled because merchants were slow to join. Businesses were often required to invest in new Point of Sale (POS) hardware without clear incentives.
Recommendations:
- Lower Barriers to Entry: BiMPay’s use of QR codes and aliases (like phone numbers) is a strong start, as it eliminates the need for expensive card readers.
- Address Cash Flow Directly: The government must highlight BiMPay’s Instant Settlement as its primary selling point for small businesses. In a cash-based economy, a vendor who can access their funds in 10 seconds rather than waiting for a bank clearing cycle has a massive competitive advantage.
Enforce “Radical Interoperability”
DCash suffered when commercial banks were slow to integrate, creating “walled gardens” where users couldn’t send money across different institutions.
Recommendations:
- Mandatory Participation: The CBB has already taken the vital step of making BiMPay a foundational rail that integrates with all banks and existing digital wallets.
- Level the Playing Field: The government must ensure that smaller fintechs and credit unions can offer services on par with larger commercial banks. This competition will lower costs for the end-user and drive innovation in the digital wallet space.
Build Trust in the Platform
Previous initiatives often mistook a lack of adoption for a “natural disinterest” in digital tools. In reality, users were simply worried about security, privacy, and resilience.
Recommendations:
- Be Transparent About Privacy: Explicitly detail what data is collected and why. Following the lessons of the Sand Dollar, the government should clarify why certain tiers of wallets require identification while others do not.
- Showcase Security: BiMPay uses multi-factor authentication (MFA) and other layered security controls. Educational campaigns should not just say the system is “secure,” they should demonstrate how these features protect the user’s money. Furthermore, awareness building must be continuous throughout the lifecycle of BiMPay, because treating security as a “one-and-done” fails to account for human psychology and the fast-moving nature of digital threats.
- Fraud Prevention: The CBB must embed strict, real-time fraud monitoring natively into the central infrastructure of BiMPay to address critical risks like transaction irrevocability, social engineering, phishing, money laundering, and ultimately to preserve sovereign digital trust.
- Redundancy & Resilience: To prevent a prolonged outage like DCash (54 days), BiMPay must implement an active-active infrastructure across geographically dispersed data centers to provide real-time failover, and network diversification through multiple telecom providers to mitigate localized disruptions. Furthermore, BiMPay should incorporate offline payment capabilities to maintain transaction continuity during Internet or power outages. Regular, mandatory failover testing and continuous health monitoring across all participating financial institutions are essential to maintaining operational resilience.
The WeChat/Grab Model: Building a “Super App” Ecosystem
The most successful peer-to-peer (P2P) platforms, like China’s WeChat and Southeast Asia’s Grab, succeeded because they became “lifestyle companions.” They didn’t just move money; they integrated daily necessities.
Recommendations:
- Social Integration: WeChat succeeded because it integrated payments directly into the messaging app people were already using. BiMPay must ensure that sending money is as easy as sending a WhatsApp message.
- The “Network Effect”: The government must incentivize anchor institutions such as utilities, supermarkets, and gas stations to offer BiMPay-exclusive discounts or loyalty rewards.
- In-App Ecosystem Mini Programs: BiMPay should open its API to allow local businesses to build mini-programs directly into the BiMPay wallet environment. For example, a user could open the BiMPay app, order food from Chefette or another local restaurant, buy a ticket to a Crop Over event, or pay for a taxi, and complete the entire transaction securely via the built-in payment rail without ever leaving the ecosystem.
- Alternative Credit Scoring: Many unbanked Barbadians struggle to secure financing because they lack a formal credit history. BiMPay could safely aggregate user transaction histories (with strict user consent and privacy controls overseen by the Data Protection Commissioner) to allow local credit unions or fintech lenders to offer micro-loans or flexible insurance policies directly inside the app, based on the user’s real digital footprint rather than rigid banking metrics.
- Peer-to-Peer Group Splitting and Local Gifting: BiMPay should feature a highly intuitive peer-to-peer (P2P) tool that allows users to seamlessly split dinner bills, crowdsource funding (local version of GoFundMe), or tip local musicians and hospitality workers seamlessly.
Strategic Integration: The Bridge to PayPal, Google, and Apple
For a tourism-dependent economy like Barbados, isolation is the enemy of growth. While BiMPay is a domestic solution, its long-term success depends on its ability to talk to the world.
Why Global Integration Matters:
- Tourism Tension: A tourist from New York or London shouldn’t have to download a “Barbados-only” app. Future integration with Google Pay and Apple Pay via the BiMPay rail would allow visitors to spend seamlessly at local vendors who currently can’t afford expensive merchant terminals.
- The Remittance Lifeline: Integration with PayPal would revolutionize how the Barbadian diaspora sends money home. By allowing a PayPal transfer to settle instantly into a BiMPay wallet, the government removes the predatory fees and multi-day delays of traditional remittance services.
Tactical Recommendations for the Government of Barbados
To avoid the fate of the Sand Dollar, the Government must execute on five specific pillars:
Use “G2P” as the Adoption Engine
The government is the nation’s largest payor. To drive adoption, all Government-to-Person (G2P) payments, including pensions, welfare, tax refunds, and student grants, should be defaulted to BiMPay wallets. When 50,000 citizens have “digital money” in their pockets on the first of the month, merchants will be forced to accept it.
Mandate Interoperability
The Central Bank must ensure that the BiMPay Interoperability Hub is truly open. No bank should be allowed to close off its customers. A user with a wallet from a small credit union must be able to send money to a user at a large commercial bank with zero friction.
Zero-Cost Merchant Onboarding
The government should subsidize the “last mile” for small businesses. This includes providing free QR code signage and ensuring that the merchant transaction fees for BiMPay are significantly lower than traditional credit card fees (which can reach 3-5% in the region).
Allow Users to Quickly and Conveniently “Cash Out”
Users must not be locked into a digital ecosystem without access to traditional cash. BiMPay should allow users to get physical cash back at any merchant location, reducing dependency on automated teller machines (ATMs).
Privacy-First Communication
Transparency is the only cure for skepticism. The government must effectively communicate that BiMPay uses robust privacy-enabling controls and that, while the system is audited for fraud, it is not a tool for granular government surveillance of lawful private spending.
Operational Independence
To operate most effectively, I recommend that that the government convert BiMPay into an independent public-private corporate structure (somewhat akin to what Denmark has done with NemKonto).
Under this model, the Central Bank retains ownership of the invisible “underground pipe” (the payment rail) to ensure safety and neutrality, but hands day-to-day operations, marketing, and developer relations over to a dedicated, agile management team that operates outside the slow-moving framework of standard civil service.
Recommendations:
- Technical Agility and Speed: A separate, dedicated corporate entity operates outside the rigid hiring and procurement frameworks of civil service. It can recruit specialized, top-tier cybersecurity and software engineers at market rates, ensuring rapid software updates and preventing prolonged system overshoots like the DCash outage.
- Dedicated Service Focus: Freed from managing monetary policy, an independent operational team can focus entirely on customer onboarding, merchant marketing, 24/7 technical support, and building open APIs for local fintech startups.
- Regulatory Neutrality: Spinning off the day-to-day operations ensures that the Central Bank of Barbados can act as a strictly neutral referee. It eliminates conflicts of interest, allowing the CBB to regulate the national payment rail objectively without favoring its own digital wallet product over private innovations.
The Collaborative Layer: The BiMPay Forum
To avoid operating in an authoritarian vacuum, the CBB should establish a BiMPay Forum. This would be a permanent, institutional governance and oversight body.
Recommendations:
- Plurality & Representation: The Forum would include representatives from traditional commercial banks, credit unions, fintech startups, payment institutions, business associations, consumer groups, academia, and the technical community.
- Working Groups: The governance framework would utilize specialized sub-committees to improve on the platform. These groups would collaborate on structural components like:
- Business Models: Designing new transaction methods (e.g., recurring bills).
- Technical Requirements: Mapping security standards and message formats.
- Audit & Risk: Dedicated to updating anti-fraud mechanisms, maintaining regulatory compliance, upholding privacy rights, and the monitoring and remediation of other material risks.
Conclusion: Beyond 12 June 2026
BiMPay has the potential to be the most significant upgrade to the Barbadian economy since independence. However, as the failures of the Sand Dollar and DCash have shown, “if you build it, they will come” does not apply to digital finance.
The Government of Barbados must act as an ecosystem curator, not just a software deployer. By focusing on merchant instant-settlement, mandating bank interoperability, and building a roadmap for integration with global giants like Apple, Google and PayPal, Barbados can turn BiMPay from a local project into a global standard for digital excellence.
In the digital age, Instant Matters. And not just for convenience, but for the very survival of the Caribbean economy.